Why cloud security breaches take days longer to investigate than on-premises attacks
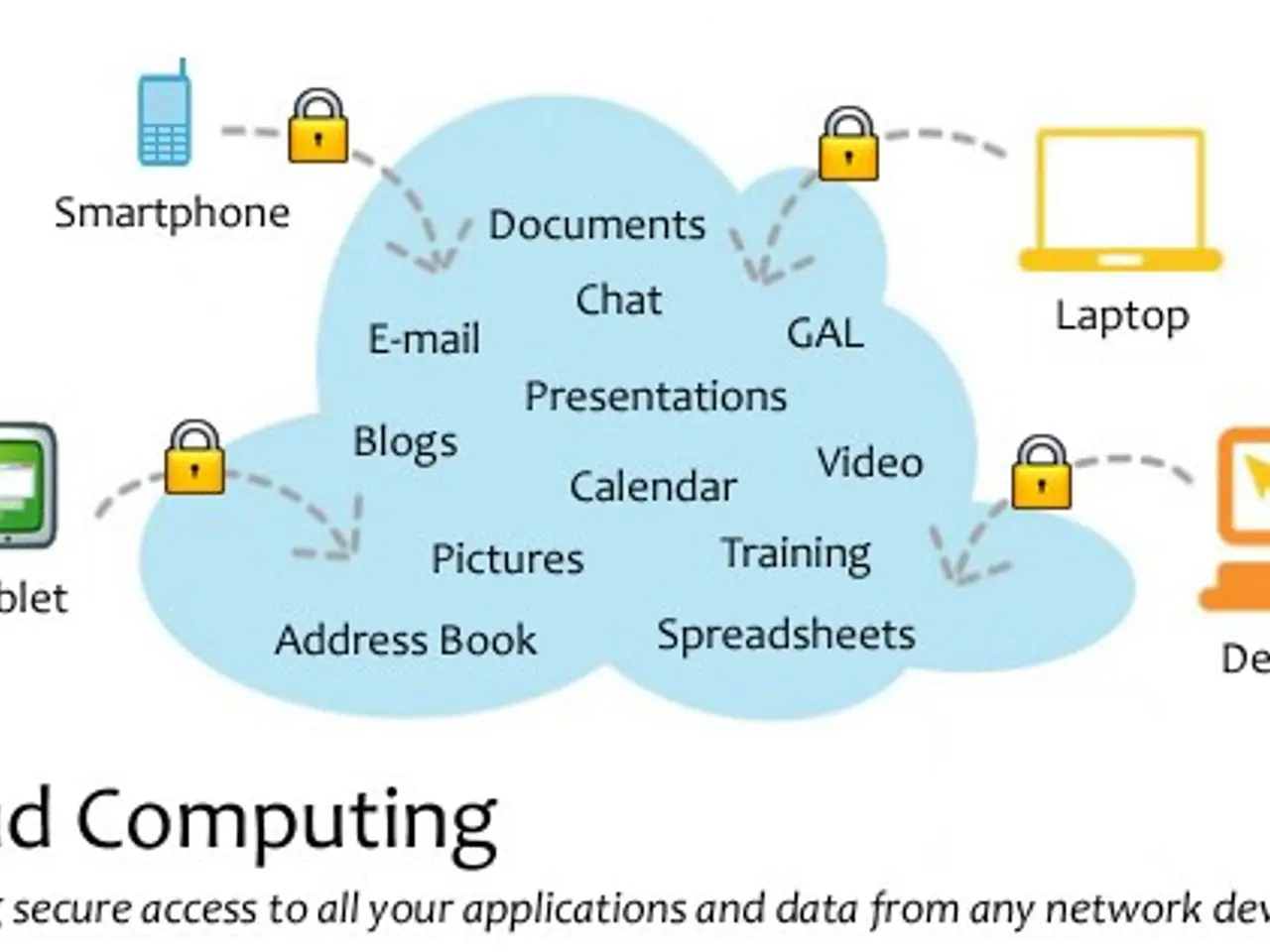
Cloud-based systems now form the backbone of modern IT, but their dynamic and scalable nature creates fresh challenges for security teams. Investigating threats in these environments often takes days longer than traditional on-premises breaches, leaving gaps where evidence can slip through.
Security teams face growing difficulties when tracking threats in ephemeral, serverless cloud setups. The sheer volume of vulnerabilities—over 43,000 recorded in 2024 alone—adds pressure, with nearly half deemed high-risk. Attackers increasingly deploy novel, hard-to-detect methods, making it tougher to piece together incidents after they occur.
Traditional forensic methods rely on manual checks and isolated data points, which often fail to capture critical evidence. Cloud incidents, on average, take three to five days longer to analyse than on-premises breaches. This delay stems from the complexity of tracing activity across fleeting virtual environments. Automated forensic tools offer a faster solution. By integrating them with detection and response systems, teams can generate a forensic timeline within minutes. Darktrace, for example, has built a system that automatically preserves relevant data the moment an alert triggers. Such automation not only speeds up investigations but also uncovers structural security weaknesses, aiding post-incident recovery.
The shift to automated cloud forensics could cut investigation times from days to minutes. With threats growing more sophisticated, faster data collection and analysis will help teams respond before evidence disappears. For now, the gap between detection and action remains a key hurdle for security operations.
Read also:
- Ignorant Youth Unfamiliar with Quebec's Cultural Landscape
- PCOS-related Gas Buildup: Explanation, Control Strategies, and Further Insights
- Astral Lore and Celestial Arrangements: Defining Terms & In-Depth Insights - Historical Accounts & Glossary of Cosmic Mythology
- "Rural Idyls with Supercars: Astonishing Sites Where Residents Cruise McLarens and Ferraris for Groceries"